Who we are
Nice to meet you
As a global asset manager, we center our solutions around your needs. We’re driven by endless curiosity, rigorous research and a proven passion for sustainability, and we’ll guide you towards ground-breaking active investment strategies.
Interested in investing for today and tomorrow’s needs? Having our investments contribute to a healthy planet and society is our common goal. Let’s share the conversation: talk to one of our colleagues.






 Yearly Outlook
Yearly Outlook Robeco Active ETFs
Robeco Active ETFsActive ETFs for today’s investors
Our latest insights
Opportunities
We are pleased to highlight some opportunities selected by our experts.
A taste of our products
QI Global Developed 3D Enhanced Index Equities
Systematic and sustainable factor approach as an alternative to passive investing

Emerging Stars Equities
Investing in emerging economies based on top-down country analysis and bottom-up stock selection

Credit Income
Targeting a consistent level of income by investing in companies that contribute to the SDGs


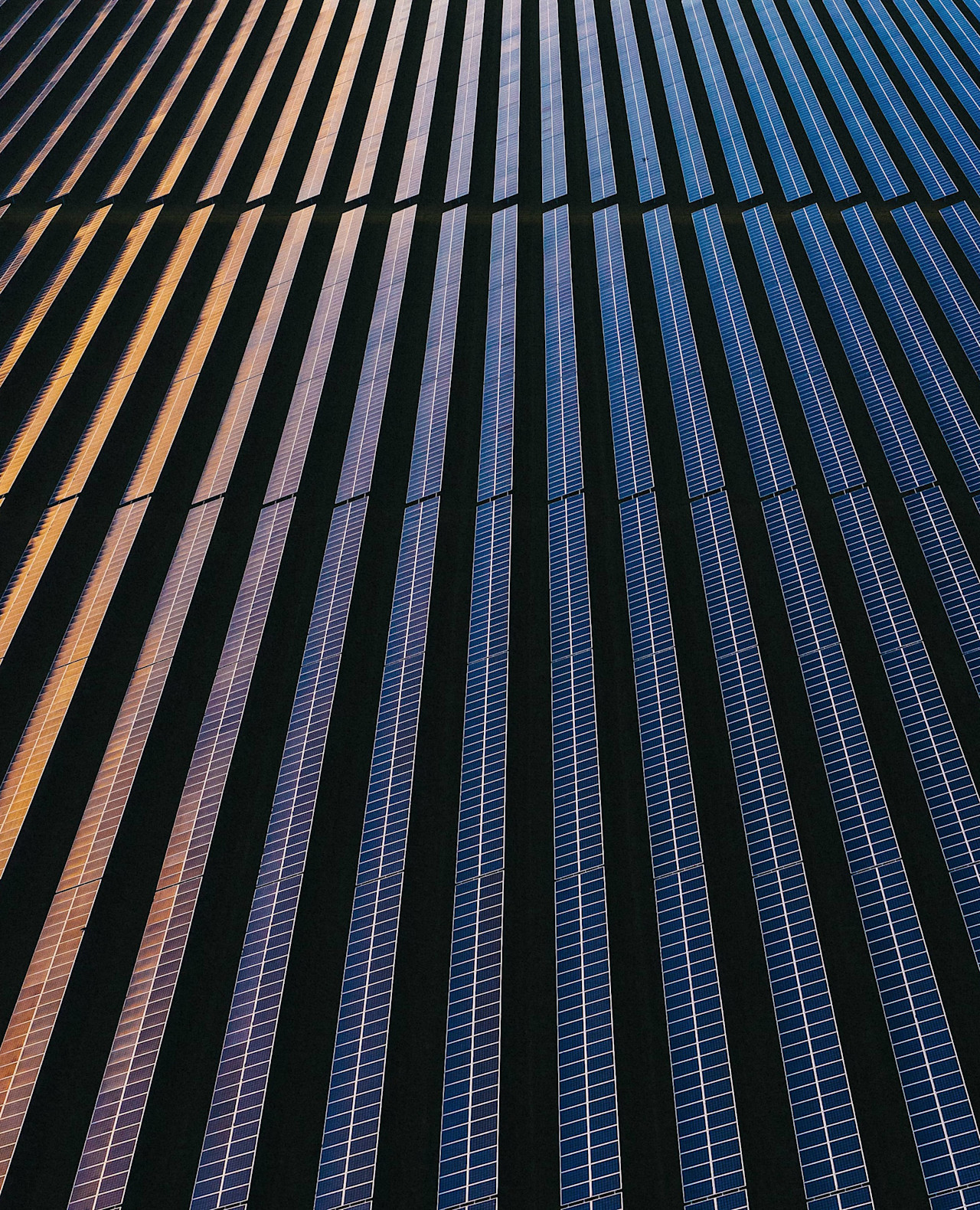
Climate Euro Government Bond UCITS ETF
A novel investment solution aligning sovereign debt portfolio with climate action